As soon as behind the captive portal, the web page initiates the Home windows Check Connectivity Standing Indicator, a authentic service that determines whether or not a tool has Web entry by sending an HTTP GET request to hxxp://www.msftconnecttest[.]com/redirect. That website, in flip, redirects the browser to msn[.]com. As Thursday’s submit defined:
As soon as the system opens the browser window to this tackle, the system is redirected to a separate actor-controlled area that seemingly shows a certificates validation error which prompts the goal to obtain and execute ApolloShadow. Following execution, ApolloShadow checks for the privilege stage of the ProcessToken and if the system isn’t operating on default administrative settings, then the malware shows the person entry management (UAC) pop-up window to immediate the person to put in certificates with the file title CertificateDB.exe, which masquerades as a Kaspersky installer to put in root certificates and permit the actor to achieve elevated privileges within the system.
The next diagram illustrates the an infection chain:
ApolloShadow invokes the GetTokenInformationType API to examine if it has ample system rights to put in the foundation certificates. If not, the malware makes use of a complicated course of that spoofs a web page at hxxp://timestamp.digicert[.]com/registered, which in flip sends the system a second-stage payload within the type of a VBScript.
As soon as decoded, ApolloShadow relaunches itself and presents the person with a Person Entry Management window looking for to raise its system entry. (Microsoft offered many extra technical particulars concerning the method in Thursday’s submit.)
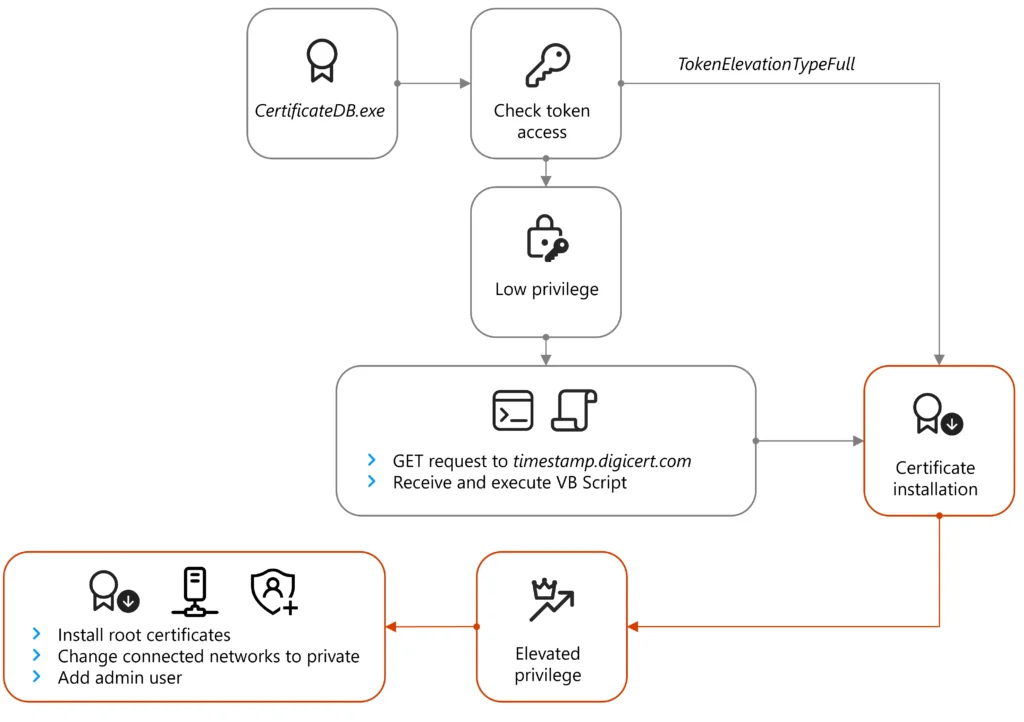
If ApolloShadow already has ample system rights, the malware configures all networks the host connects to as non-public.
“This induces a number of modifications together with permitting the host system to develop into discoverable and enjoyable firewall guidelines to allow file sharing,” Microsoft defined. “Whereas we didn’t see any direct makes an attempt for lateral motion, the primary motive for these modifications is more likely to scale back the issue of lateral motion on the community.” (The Microsoft submit additionally offered technical particulars about this method.)
Microsoft mentioned the flexibility to trigger contaminated units to belief malicious websites permits the menace actor to keep up persistence, seemingly to be used in intelligence assortment.
The corporate is advising all clients working in Moscow, significantly delicate organizations, to tunnel their visitors by means of encrypted tunnels that hook up with a trusted ISP.









