[ad_1]
From the Division of Weird Anomalies: Microsoft has suppressed an unexplained anomaly on its community that was routing visitors destined to instance.com—a website reserved for testing functions—to a maker of electronics cables situated in Japan.
Below the RFC2606—an official normal maintained by the Web Engineering Activity Drive—instance.com isn’t obtainable by any get together. As a substitute it resolves to IP addresses assigned to Web Assiged Names Authority. The designation is meant to forestall third events from being bombarded with visitors when builders, penetration testers, and others want a website for testing or discussing technical points. As a substitute of naming an Web-routable area, they’re to decide on instance.com or two others, instance.internet and instance.org.
Misconfig gone, however is it fastened?
Output from the terminal command cURL reveals that gadgets inside Azure and different Microsoft networks have been routing some visitors to subdomains of sei.co.jp, a website belonging to Sumitomo Electrical. Many of the ensuing textual content is precisely what’s anticipated. The exception is the JSON-based response. Right here’s the JSON output from Friday:
{"electronic mail":"electronic mail@instance.com","companies":[],"protocols":[{"protocol":"imap","hostname":"imapgms.jnet.sei.co.jp","port":993,"encryption":"ssl","username":"email@example.com","validated":false},{"protocol":"smtp","hostname":"smtpgms.jnet.sei.co.jp","port":465,"encryption":"ssl","username":"email@example.com","validated":false}]}
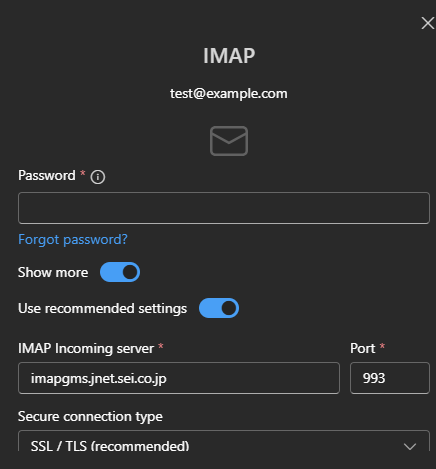
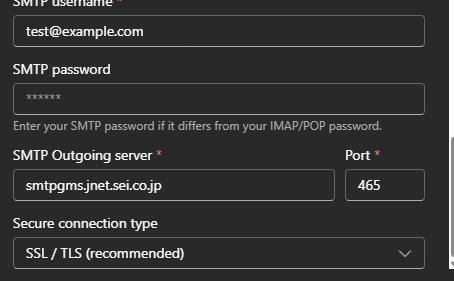
Equally, outcomes when including a brand new account for take a look at@instance.com in Outlook appeared like this:
In each circumstances, the outcomes present that Microsoft was routing electronic mail visitors to 2 sei.co.jp subdomains: imapgms.jnet.sei.co.jp and smtpgms.jnet.sei.co.jp. The conduct was the results of Microsoft’s autodiscover service.
“I’m admittedly not an knowledgeable in Microsoft’s inner workings, however this seems to be a easy misconfiguration,” Michael Taggart, a senior cybersecurity researcher at UCLA Well being, mentioned. “The result’s that anybody who tries to arrange an Outlook account on an instance.com area may unintentionally ship take a look at credentials to these sei.co.jp subdomains.”
When requested early Friday afternoon why Microsoft was doing this, a consultant had no reply and requested for extra time. By Monday morning, the improper routing was now not occurring, however the consultant nonetheless had no reply.
[ad_2]